Data Security Requirements for Real Estate Transactions
Real estate transactions involve the exchange of highly sensitive personal and financial information between multiple parties. Cybercriminals frequently target these deals because they involve large sums of money and valuable data sets. Consequently, maintaining rigorous security standards is essential for protecting the interests of buyers, sellers, and lending institutions.
The transition to digital closings requires participants to manage various legal forms and disclosures in a secure environment. Many professionals now teach clients how to esign a pdf to ensure that sensitive documents are handled with modern encryption. This digital approach reduces the risk of physical mail interception and provides a clear audit trail for every signature.
Technical Security Standards
Technical safeguards prevent the unauthorized interception of mortgage applications and title documents. Implementation of the following cryptographic standards and authentication protocols ensures data integrity during modern property transfers.
End-to-End Encryption
AES 256-bit encryption serves as the industry standard for securing data at rest and in transit. This symmetric-key algorithm uses a 256-bit key to encrypt data, making it computationally infeasible for brute-force attacks. Transport Layer Security (TLS) 1.3 protects communication channels by establishing encrypted links between web servers and browsers.
Multi-Factor Authentication
Passwords alone fail to secure access to escrow accounts and private portals. Robust systems implement Time-based One-Time Passwords (TOTP) or FIDO2 hardware security keys to verify user identity. These methods require a physical device or a temporary code, which negates the effectiveness of stolen or phished credentials.
Secure File Sharing
Standard email lacks the encryption necessary for sending Social Security numbers or bank statements. Secure File Transfer Protocol (SFTP) and specialized portals provide encrypted tunnels for document exchange. These platforms use granular access controls to restrict file visibility to specific IP addresses or authenticated user roles.
Regular Security Audits
System integrity relies on frequent vulnerability assessments and penetration testing. SOC 2 Type II reports provide independent verification that a service provider maintains strict information security policies. Frequent patch management cycles ensure that software vulnerabilities are addressed within 48 hours of discovery.
Regulatory and Legal Compliance
Federal and state laws impose strict requirements on how real estate professionals handle and store consumer data. Organizations must adhere to these legal frameworks to avoid severe penalties and protect their reputation in the marketplace.
Gramm-Leach-Bliley Act
The Gramm-Leach-Bliley Act requires financial institutions to explain their information-sharing practices to their customers. Real estate entities that provide settlement services must implement a comprehensive written information security program. This program protects non-public personal information from unauthorized access or use.
Data Privacy Regulations
State-level laws like the California Consumer Privacy Act grant individuals greater control over their personal information. Real estate firms must provide clear notice about what data they collect and allow clients to request its deletion. Compliance involves maintaining detailed records of data processing activities and third-party sharing.
Record Retention Rules
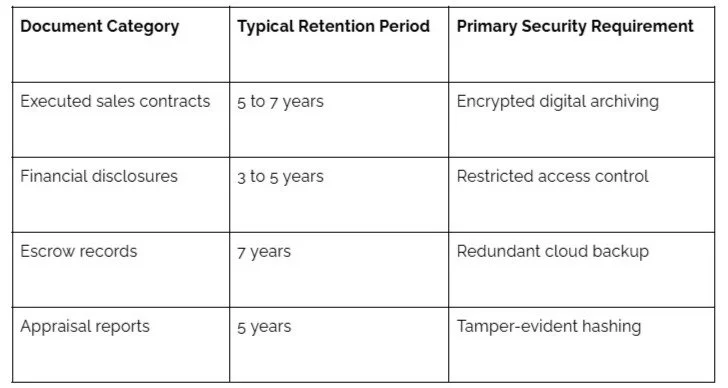
Legal agreements and financial records must be stored securely for specific periods mandated by state licensing boards. The following table summarizes the typical retention requirements and security expectations for various real estate document categories:
Operational Risk Management
Security requires strict internal procedures and employee vigilance. Effective data protection relies on the human element and the prevention of social engineering tactics.
Wire Fraud Prevention
Scammers send fraudulent emails to buyers containing fake wiring instructions to divert closing funds. Title companies verify all financial instructions via a secondary, out-of-band communication channel such as a known phone number. Furthermore, digital portals now host wiring details behind encrypted login screens to prevent email spoofing.
Employee Security Training
Staff members undergo training to recognize phishing attempts that target sensitive client information. The core components of a modern real estate security training program:
Recognition of URL typosquatting and deceptive sender headers.
Proper management of hardware-based security keys and password managers.
Implementation of clean-desk policies for physical document protection.
Immediate reporting procedures for suspected system breaches or lost devices.
Third-Party Vendor Management
Real estate firms vet the security practices of appraisers and inspectors before sharing project folders. Service-level agreements must include mandatory data breach notification periods, often set at 24 to 72 hours. Moreover, vendors only receive the minimum level of access required to perform their specific tasks.
Secure Document Disposal
Physical copies of sensitive documents must undergo cross-cut shredding to prevent reconstruction. Digital files require a multi-pass wipe of the storage media to ensure data cannot be recovered via forensic tools. These procedures prevent the exposure of private data after hardware decommissioning.
Strategic Governance Results
Maintaining high security standards builds trust with clients during one of the most significant financial events of their lives. Consistency in technical and operational safeguards protects the financial stability of the real estate industry. Strategic investment in data security is a fundamental requirement for any professional operating in the modern market.